WPS or Wifi Protected Setup also can be known as Push 'N' Connect, and QSS, Quick Secure Setup. This was introduced in 2007, and was created in an effort to make router setup easier for the general public. Instead of finding the SSID of the network and entering the password to connect to the internet, simply use WPS to connect with a network. That's it, simple, easy, and originally thought to be secure.
There are four different methods of using WPS:
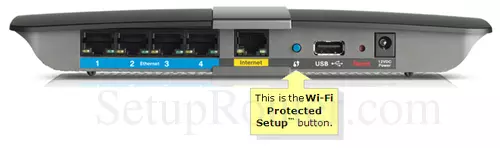
- PBC or Push Button Configuration method- This normally a physical button, on the back of your router. It should look something like this:

All you need to do to connect with the network is simultaneously push the WPS button on both, the router and the device you want to be connected. This definitely makes network setup child's play.
-
PIN method- All routers that support WPS are required to have this method. It may be in addition to another method or alone. For this method, there is an eight digit PIN number, usually located on the back of the router, that you enter on the device or computer you want to join your network.
-
NFC or Near Field Communication method- where you simply touch the devices to the router that you want to connect, and you are connected to that network.
-
USB method- in which you use a USB flash drive to connect the two devices.
Is WPS Secure
In 2011, a major design flaw was found in the PIN method of WPS, which is mandatory for all WPS enabled products. Instead of the entire eight digit PIN being validated by the router, it separates it into two, four digit PINS. This makes it very easy to crack because there are only 11,000 different possible 4 digits combinations available, as opposed to 100,000,000 different combinations for eight numbers. Within a matter of hours an attacker can have access to your network using a type of attack called brute force. Brute force attacks are a way of very quickly checking every possible combination.
To combat this lack of security, some router companies have begun to install a lock out period. This means that after several failed attempts you are locked out for a specific amount of time from using the PIN. You can use the push button method as this is still considered relatively secure. Some companies are recommending you turn off the PIN method altogether.
Turn WPS Off
By default the WPS on your router is on, meaning that even if you never used it, it is still on and waiting. Therefore ignoring it as some have suggested, does little to stop anyone determined to hack your system. You need to manually turn it off. In some cases you need a firmware update that allows for shutting off the WPS or initializing a lock out period.
WPS is a feature that, due to the PIN method is highly vulnerable to outside attacks. We strongly recommend that you disable this function if you can. If you are unable to do this, we recommend checking for a firmware upgrade that allows for a lock out period or turning WPS off completely.